Good report card but data breaches are up, with no sign of letting up
By Cameron Abbott, Rob Pulham, Stephanie Mayhew and Dadar Ahmadi-Pirshahid
[Featured image from a linkedin post of Office of the Australian Information Commissioner made on 3 March 2023]Shortly after the Government announced their ambition to make Australia a global leader in cyber security, Australia has been named the country with “the greatest progress and commitment toward creating a cyber defence environment” in MIT’s Cyber Defence Index of 2022/23.
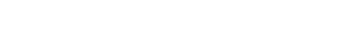
However, the Office of the Australian Information Commissioner’s latest notifiable data breaches report paints a different picture. The Commissioner reported a 26% increase in the number of total reported data breaches and a 41% increase in the number of reported data breaches arising from malicious or criminal attacks compared with the first half of 2022. Health service providers and the finance sector were the worst hit, together representing almost a third of reported data breaches.
In releasing the report, the Commissioner once again stressed the need for organisations to collect only the minimum amount of personal information required and deleting it when it is no longer needed. In the report the Commissioner has recommended a number of steps to address the kinds of issues featured in the second half of 2022, including:
Read More